Hackers have wife interracial sex videodiscovered a new way to remotely take control of your computer — all through the Google Chrome web browser.
A report from cybersecurity company SquareX lays out the new multifaceted cyberattack, which the firm has dubbed "browser syncjacking."
At the core of the attack is a social engineering element, as the malicious actor first must convince the user to download a Chrome extension. The Chrome extension is usually disguised as a helpful tool that can be downloaded via the official Chrome Store. It requires minimal permissions, further cementing its perceived legitimacy to the user. According to SquareX, the extension actually does usually work as advertised, in order to further disguise the source of the attack from the user.
Meanwhile, secretly in the background, the Chrome extension connects itself to a managed Google Workspace profile that the attacker has set up in advance. With the user now unknowingly signed into a managed profile, the attacker sends the user to a legitimate Google support page which is injected with modified content through the Chrome extension, telling the user they need to sync their profile.
When the user agrees to the sync, they unwittingly send all their local browser data, such as saved passwords, browsing history, and autofill information, to the hacker's managed profile. The hacker can then sign into this managed profile on their own device and access all that sensitive information.
The attack up to this point already provides the hacker with enough material to commit fraud and other illicit activities. However, browser syncjacking provides the hacker with the capability to go even further.
Using the teleconferencing platform Zoom as an example, SquareX explains that using the malicious Chrome extension, the attacker can send the victim to an official yet modified Zoom webpage that urges the user to install an update. However, the Zoom download that's provided is actually an executable file that installs a Chrome browser enrollment token from the hacker's Google Workspace.
After this occurs, the hacker then has access to additional capabilities and can gain access to the user's Google Drive, clipboard, emails, and more.
The browser syncjacking attack doesn't stop there. The hacker can take one further step in order to not just take over the victim's Chrome profile and Chrome browser, but also their entire device.
Through that same illicit download, such as the previously used Zoom update installer example, the attacker can inject a "registry entry to message native apps" by weaponizing Chrome’s Native Messaging protocol. By doing this, the attacker basically sets up a connection "between the malicious extension and the local binary." Basically, it creates a flow of information between the hacker's Chrome extension and your computer. Using this, the hacker can send commands to your device.
What can the hacker do from here? Pretty much anything they want. The attacker will have full access to the user's computer files and settings. They can create backdoors into the system. They can steal data such as passwords, cryptocurrency wallets, cookies, and more. In addition, they can track the user by controlling their webcam, take screenshots, record audio, and monitor everything input into the device.
As you can see, browser syncjacking is nearly completely unrecognizable as an attack to most users. For now, the most important thing you can do to protect yourself from such a cyberattack is to be aware of what you download and only install trusted Chrome extensions.
Topics Cybersecurity Google
 Obama photographer Pete Souza on Trump: 'We failed our children'
Obama photographer Pete Souza on Trump: 'We failed our children'
 Ye Olde Grease Lightning, and Other News by Sadie Stein
Ye Olde Grease Lightning, and Other News by Sadie Stein
 The best conspiracy theory podcasts about dangerous misinformation
The best conspiracy theory podcasts about dangerous misinformation
 Driving Mr. Murray by Tony Scherman
Driving Mr. Murray by Tony Scherman
 Wordle today: The answer and hints for January 28, 2025
Wordle today: The answer and hints for January 28, 2025
 Notes from a Bookshop: Late Summer, or Summer Is a Kind of Island by Kelly McMasters
Notes from a Bookshop: Late Summer, or Summer Is a Kind of Island by Kelly McMasters
 Lessons from an Eleven
Lessons from an Eleven
 William Faulkner’s Unexpected Art, and Other News by Sadie Stein
William Faulkner’s Unexpected Art, and Other News by Sadie Stein
 In Paris Agreement speech, Trump never acknowledged the reality of global warming
In Paris Agreement speech, Trump never acknowledged the reality of global warming
 Drinking with Salinger by Sadie Stein
Drinking with Salinger by Sadie Stein
 Cibao FC vs. Guadalajara 2025 livestream: Watch Concacaf Champions Cup for free
Cibao FC vs. Guadalajara 2025 livestream: Watch Concacaf Champions Cup for free
 Tolstoy Goes Digital, and Other News by Sadie Stein
Tolstoy Goes Digital, and Other News by Sadie Stein
 Wordle today: Here's the answer and hints for July 11
Wordle today: Here's the answer and hints for July 11
 The Snack by Molly Hannon
The Snack by Molly Hannon
 How to quit social media: This Gen Z
How to quit social media: This Gen Z
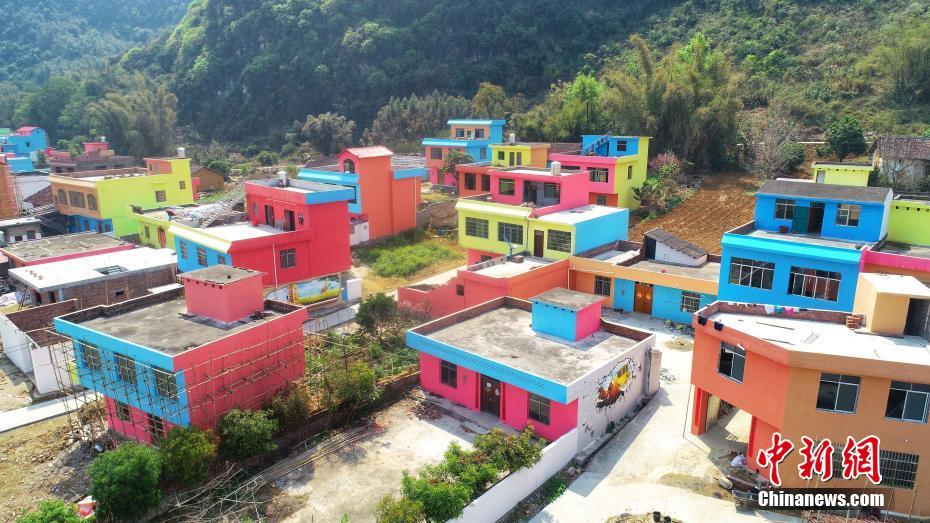
 Lidija Dimkovska, Skopje, Macedonia by Matteo Pericoli
Lidija Dimkovska, Skopje, Macedonia by Matteo Pericoli
 Have Questions About The Paris Review? Ask Our Editors on Reddit! by The Paris Review
Have Questions About The Paris Review? Ask Our Editors on Reddit! by The Paris Review
 Emmy nominations 2023: How and when to watch
Emmy nominations 2023: How and when to watch
 Houston Rockets vs. Dallas Mavericks 2025 livestream: Watch NBA online
Houston Rockets vs. Dallas Mavericks 2025 livestream: Watch NBA online
 Drinking with Salinger by Sadie Stein
Drinking with Salinger by Sadie Stein
Apple backs marriage equality campaign in AustraliaDavid Bowie approved his 'Twin Peaks: The Return' cameo before he diedHappy 25th birthday, Harley Quinn. Your creator still loves youApple tried to show off Face ID, and it was so embarrassing'Frozen' star Kristen Bell gave a live update on Hurricane Irma from her hotel roomAmazon's next Fire TV device rumored to act like a superGet ready for a Trump book from your favorite White House reportersThe 8 biggest questions we still have about Apple's new iPhonesThe 8 biggest questions we still have about Apple's new iPhonesApple iOS 11 has a hidden security feature that cops will hateThe 2 tiny, crucial moments in 'IT' only true Stephen King fans will have spottedPlastic bags get the boot once againThe iPhone 6S is the last of the great iPhones, everything else is trashI'm so sorry, but here are Ted Cruz's favorite pornosApple's iPhone 8 comes in gold, but everyone's calling it pinkEven Apple admits Face ID can't fully secure your sensitive dataPatty Jenkins will direct 'Wonder Woman' sequelChrissy Teigen loves 'Gogglebox' now and Brits are going wild for itGood lord, please get this snake off the subwayHere's why the Apple Store just went down Wordle today: Here's the answer and hints for June 11 Allen Ginsberg Snaps, and Other News by Sadie Stein “Psalm 139” by Lorin Stein 'Elemental' review: A fiery immigration narrative and a rom Conspiracy Theories, and Other News by Sadie Stein Hilarious Pennsylvania memes flood Twitter after Biden takes lead The Fitzgerald Sharon Olds, “Diagnosis” by Sadie Stein Source of All Joy: On Alina Szapocznikow by Yevgeniya Traps Discipline and Punish by Arthur Holland Michel Gertrude Stein, Monster Hunter, and Other News by Sadie Stein Climate activist Greta Thunberg participates in her last school strike The sustainable fashion pioneer behind drag's defiantly absurdist turn Reddit CEO's AMA over third Revel Yell by Sadie Stein CivilWarLand in Bad Decline: Preface by George Saunders What We’re Loving: Saintly Comics, High Relief by Sadie Stein Wordle today: Here's the answer and hints for June 10 Writing in Jewish, and Other News by Sadie Stein In Memoriam: Evan S. Connell, 1924–2013 by Lorin Stein
2.525s , 8612.8359375 kb
Copyright © 2025 Powered by 【wife interracial sex video】,Evergreen Information Network