The jocuri eroticetypical image of Chinese hackers is of operatives working for or with the tacit approval of the government, targeting valuable or sensitive data at foreign companies or government agencies.
While there are plenty of those, many in China—like hackers elsewhere—also target the laptop of their ex-boss or the smartphone of the guy in front of them at the coffee shop.
China’s criminal hacking community numbers at least 400,000 and sucks 100 billion yuan ($15 billion) out of the country’s economy each year, according to Zheng Bu, an angel investor and former executive at cybersecurity company FireEye.
“There is a large criminal ecosystem in China,” says Bryce Boland, FireEye’s chief technology officer for the Asia-Pacific region. And with government restrictions on security technology tightening, individuals and businesses can have a tough time combating the crooks.
Respondents to a 2016 PwC survey of 330 chief executive officers and IT directors of foreign and domestic companies operating inside China and Hong Kong reported a 417 percent year-over-year increase in “detected security incidents,” which can include malware, ransomware, stolen data, and other network breaches.
PwC says these hacks most often target customer databases and proprietary records and typically cost each company in Greater China about $2.6 million annually. Of 496 executives and IT professionals surveyed earlier this year by the American Chamber of Commerce in China, most said data-security threats were more significant in China than in other regions where their businesses operate.
Part of what makes China a lucrative target for hackers is the population’s rapid embrace of mobile payment technology—WeChat Wallet, Alipay, and other transaction software linked to popular social media services. More than half of Chinese consumers expect their phones to become their primary way to pay for things, PwC says. And automatic connections to Wi-Fi are common in China.
“Most people don’t check who is the real administrator of a public Wi-Fi connection,” says Mangesh Fasale, a malware analyst at security firm F-Secure. “Hackers in China often make decoy Wi-Fi access points, and if you connect to them, they can access whatever is on your phone.”
Fully 50 percent of detected institutional hacks in China and Hong Kong were inside jobs, involving former or current employees, according to PwC. In May a Chinese hacker with the Twitter handle @Shenfenzheng, which means “personal identity,” tweeted stolen personal information—including scans of official ID cards and home addresses—apparently belonging to dozens of top Communist Party officials and prominent businesspeople, including Wanda Group CEO Wang Jianlin and his son.
“It’s easy to figure out anybody’s information, whether you’re a government official or a celebrity,” the hacker tweeted. “Getting the common people’s data is like buying cabbage.”
That leak was likely an inside job, too. A police officer confirmed that at least some of the ID cards seem genuine and had come from the Ministry of Public Security’s database, which most police stations across China can access.
“Usernames, ID card information, credit card details—it’s very common for all this data to be stolen,” says Kenneth Wong, PwC’s cybersecurity head for China and Hong Kong. “There have been many incidents where people have gone to websites or trade shows and registered their personal information, and soon after, they will find all their ID information has been leaked online,” he says, often for a price.
China’s hackers have two main goals, says Lester Ross, a partner in the Beijing office of law firm WilmerHale. “First, to extort, to force a company or individual to pay money in order to resolve a problem. And second, to extract proprietary information to benefit somebody else, possibly another company or the government.”
The government’s efforts to control the internet make domestic users more vulnerable, says FireEye’s Boland. Beijing recently stepped up enforcement of a prohibition on the sale or import of hardware and mobile devices containing Trusted Platform Module microchips, used for encrypting passwords and biometric data.
“It’s the international standard, but it’s banned in China,” says Jake Parker, vice president for the U.S.-China Business Council. “As a consequence, companies must use old or untrusted technology systems to secure data. Excluding foreign IT hardware absolutely undermines security goals.”
The government has designated its own standards, but “there’s significant uncertainty over whether local encryption standards match international standards,” he says. “China’s standards are unchecked by outside parties.”
A draft of China’s pending cybersecurity law, which has been reviewed twice by the legislature and could be enacted by the end of the year, would expand the scope of hardware, network equipment, and services that must be accredited by local authorities before being used or sold in the country. The bill would also require more corporate data to be housed exclusively on servers located within China, including sensitive user information.
“China is trying to have more control over cybersecurity technology, which is not something that’s ever done to increase the quality of cybersecurity,” says John Pescatore, a director at IT training company SANS Security. “It’s always done so that a government can maintain its access through the technology.”
If the final legislation includes more stringent directives that companies operating in China use domestic cybersecurity technology, it’ll become even more difficult for companies to protect themselves, says Ross, the WilmerHale partner. “It certainly doesn’t benefit the Chinese customer, either,” he says.
 Best robot vacuum deal: Eufy Omni C20 robot vacuum and mop at record
Best robot vacuum deal: Eufy Omni C20 robot vacuum and mop at record
 Wordle today: The answer and hints for November 26
Wordle today: The answer and hints for November 26
 TikTok is bringing AI
TikTok is bringing AI
 Wordle today: The answer and hints for November 26
Wordle today: The answer and hints for November 26
 SpaceX's Starlink satellite launch in pictures
SpaceX's Starlink satellite launch in pictures
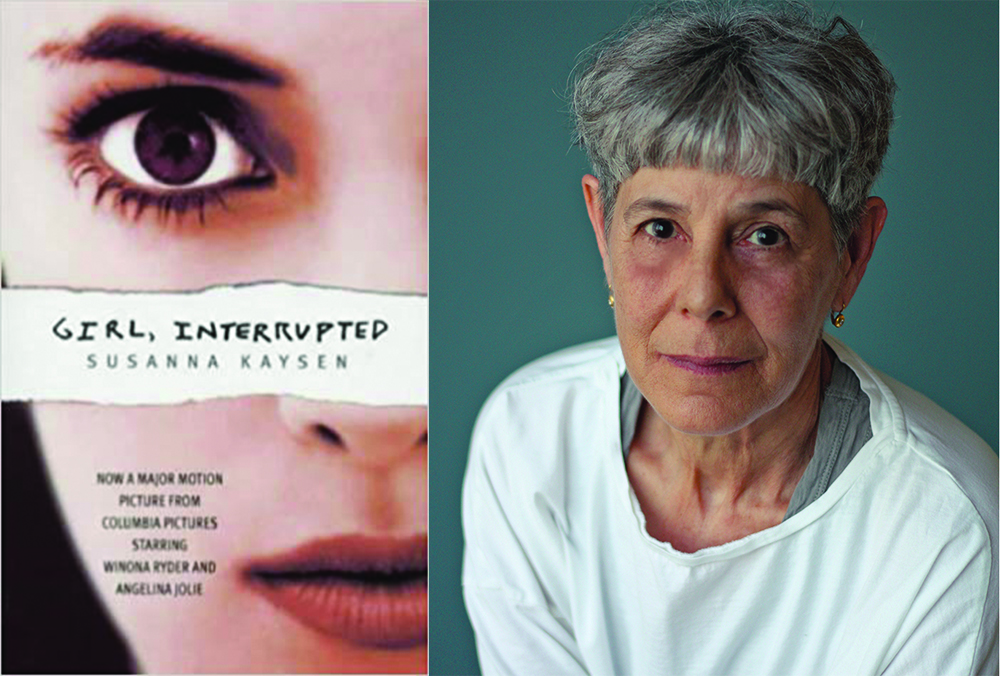 ‘Girl, Interrupted,’ Twenty
‘Girl, Interrupted,’ Twenty
 200+ best Walmart Cyber Monday deals for 2023 (live now)
200+ best Walmart Cyber Monday deals for 2023 (live now)
 Redux: Snared By Sin by The Paris Review
Redux: Snared By Sin by The Paris Review
 Is 'Sing Sing' streaming? How to watch the A24 drama at home.
Is 'Sing Sing' streaming? How to watch the A24 drama at home.
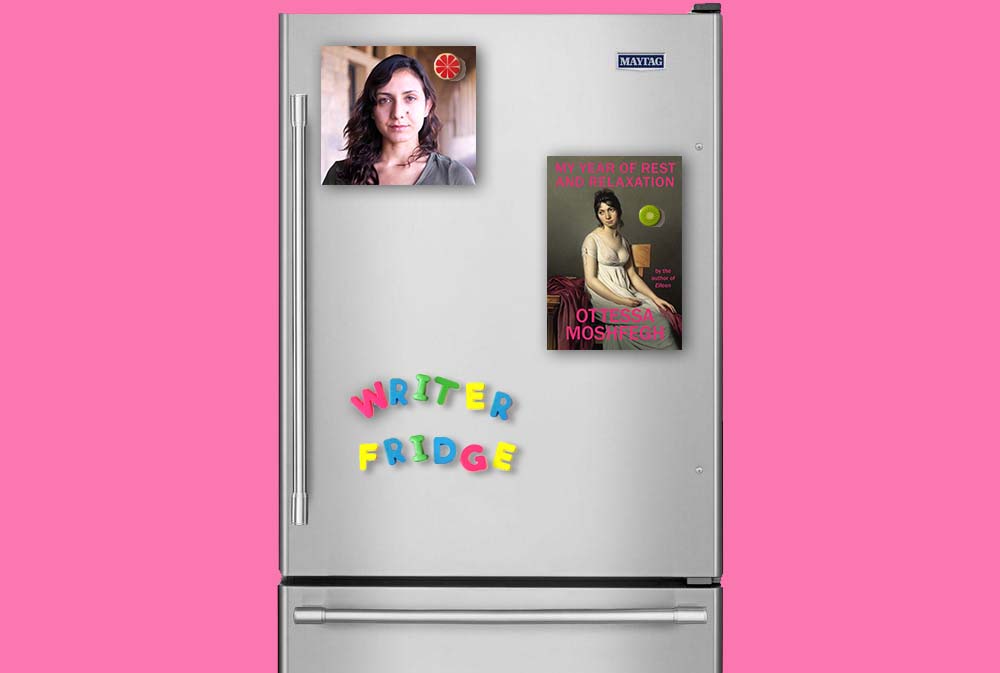 Writers’ Fridges: Ottessa Moshfegh
Writers’ Fridges: Ottessa Moshfegh
 'Severance' Reddit theory may have answered the 'Cold Harbor' mystery
'Severance' Reddit theory may have answered the 'Cold Harbor' mystery
 The Visual Frequency of Black Life by Peter L’Official
The Visual Frequency of Black Life by Peter L’Official
 Doja Cat, Lil Nas X and more 2023 Met Gala cat looks
Doja Cat, Lil Nas X and more 2023 Met Gala cat looks
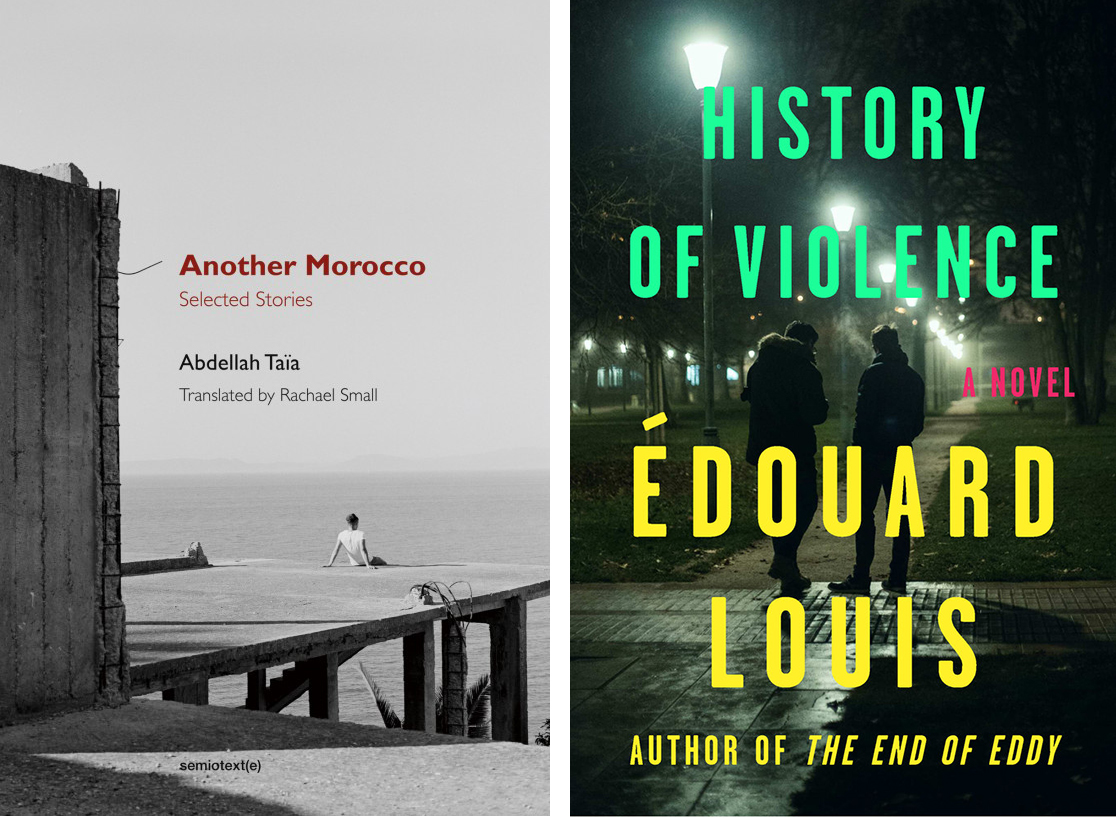 Edouard Louis and Abdellah Taïa in Conversation
Edouard Louis and Abdellah Taïa in Conversation
 Trump tariff news: See the latest impacts on consumer tech
Trump tariff news: See the latest impacts on consumer tech
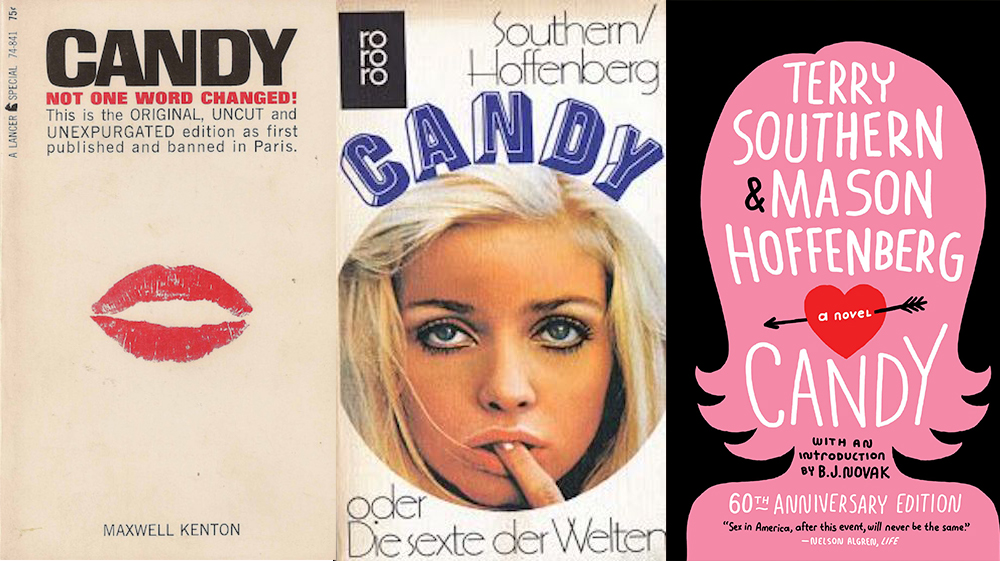 Destined for the Dirty
Destined for the Dirty
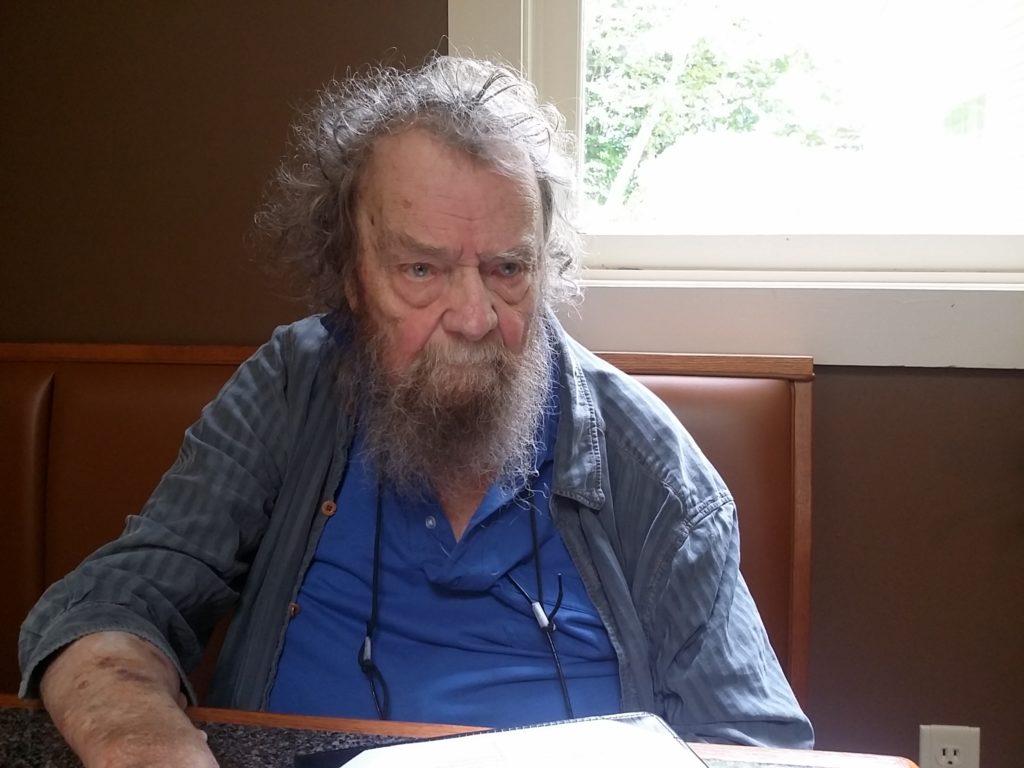 Donald Hall, Foremost God in the Harvard College Pantheon by Louis Begley
Donald Hall, Foremost God in the Harvard College Pantheon by Louis Begley
 Poetry Rx: There Will Never Be More of Summer Than There Is Now by Sarah Kay
Poetry Rx: There Will Never Be More of Summer Than There Is Now by Sarah Kay
 Best JBL deal: Save $10 on the Go 4 at Amazon
Best JBL deal: Save $10 on the Go 4 at Amazon
 Why do 'Normal People' edits still dominate TikTok?
Why do 'Normal People' edits still dominate TikTok?
Meta allows Trump back on Facebook and InstagramGoogle search has a creepy 'The Last of Us' Easter eggPaul Rudd on 'Hot Ones' is being turned into a very spicy memeJerry O'Connell tried to teach his kids about Prince and failed'Quordle' today: See each 'Quordle' answer and hints for January 27Stephen Colbert mocks Trump's absurd attempt to hold the GHow to watch 'M3GAN'Trump's latest merch is a bad ripEnjoy these delightful jackMeghan Markle opens up about the impact media scrutiny has had on herPaul Rudd on 'Hot Ones' is being turned into a very spicy meme2023 Oscar nominations: See the full listWordle today: Here's the answer, hints for January 22Who owns the moon and its precious resources?72 female MPs sign open letter condemning 'colonial' media coverage of Meghan MarkleTo Leslie' and the wordMicrosoft invests $10 billion in ChatGPT creator OpenAIIs 'Poker Face' connected to 'Knives Out'?Jim Mattis mocks Trump over 'world's most overrated general' commentsPeople are making fun of Rudy Giuliani butt Ikea's new collection for 'today's nomadic youth' has everyone very confused Joel Embiid's brilliant tweet tweaks Trump where it hurts after NBA All David Beckham hilariously trolls his son Brooklyn on Instagram live Your friends might be spying on your Facebook when you're not looking Facebook is giving longer videos a bump in your News Feed There are hidden iPad keyboards in iOS 10.3 that Apple won't let you use The LGBTQ community is coming to march and werk on Washington Trump’s political appointees will vet EPA’s scientific work before release Please leave me alone while I stare at this photo of Jupiter Google is banning Javascript attachments from Gmail Yarn shop that attacked 'vile' Pussyhat Project is getting flooded with bad Yelp reviews American Airlines is ditching seatback screens in its new planes Ronda Rousey stands in solidarity with Standing Rock by delivering supplies Great white shark gracefully photobombs 10 Dog mom jumps into freezing water to save her fur baby Madeleine Albright tweets plan to counter Trump's immigration policy Half of Americans think their cybersecurity is worse than 5 years ago Private emails are back! But this time Hillary Clinton's not involved. NYT Connections hints and answers for June 23: Tips to solve 'Connections' #743. Fighting game community is in a heated debate over teabagging
3.6179s , 8286 kb
Copyright © 2025 Powered by 【jocuri erotice】,Evergreen Information Network